Blog Contents
show
Introduction - Why Sensitive Data Makes Embedded Analytics Harder Than It Looks
Business teams want analytics inside the app they already use. Finance wants account views in workflow. Healthcare wants operational dashboards near patient systems. Regulated firms want faster decisions without extra tools. But the same dashboards that help people act faster can also expose PII, PHI, and other sensitive data if the stack is loose. That is the real tension in embedded analytics for sensitive data environments. For CEOs, CIOs, and CTOs, the problem is not just security. It is scale. If every new use case needs another analyst, admin, or security engineer, analytics turns into a staffing problem.What this article will cover
This article defines embedded analytics for sensitive data environments, names the main security and compliance pain points, and explains why YellowfinBI, through its customer-controlled and on-premises-friendly model at yellowfinbi.com, matters for teams that want to grow without adding headcount.What Embedded Analytics Means in High-Risk Data Environments
The difference between standard embedded BI and sensitive-data embedding
Standard embedded BI is mostly about convenience. Put charts in a portal. Match the UI. Keep users inside the app. Sensitive-data embedding has a stricter job. It needs data minimization, tenant isolation, auditability, row-level security, and alignment with rules such as HIPAA and GDPR. In other words, the analytics layer has to obey the app’s trust model.Why architecture matters more than dashboards
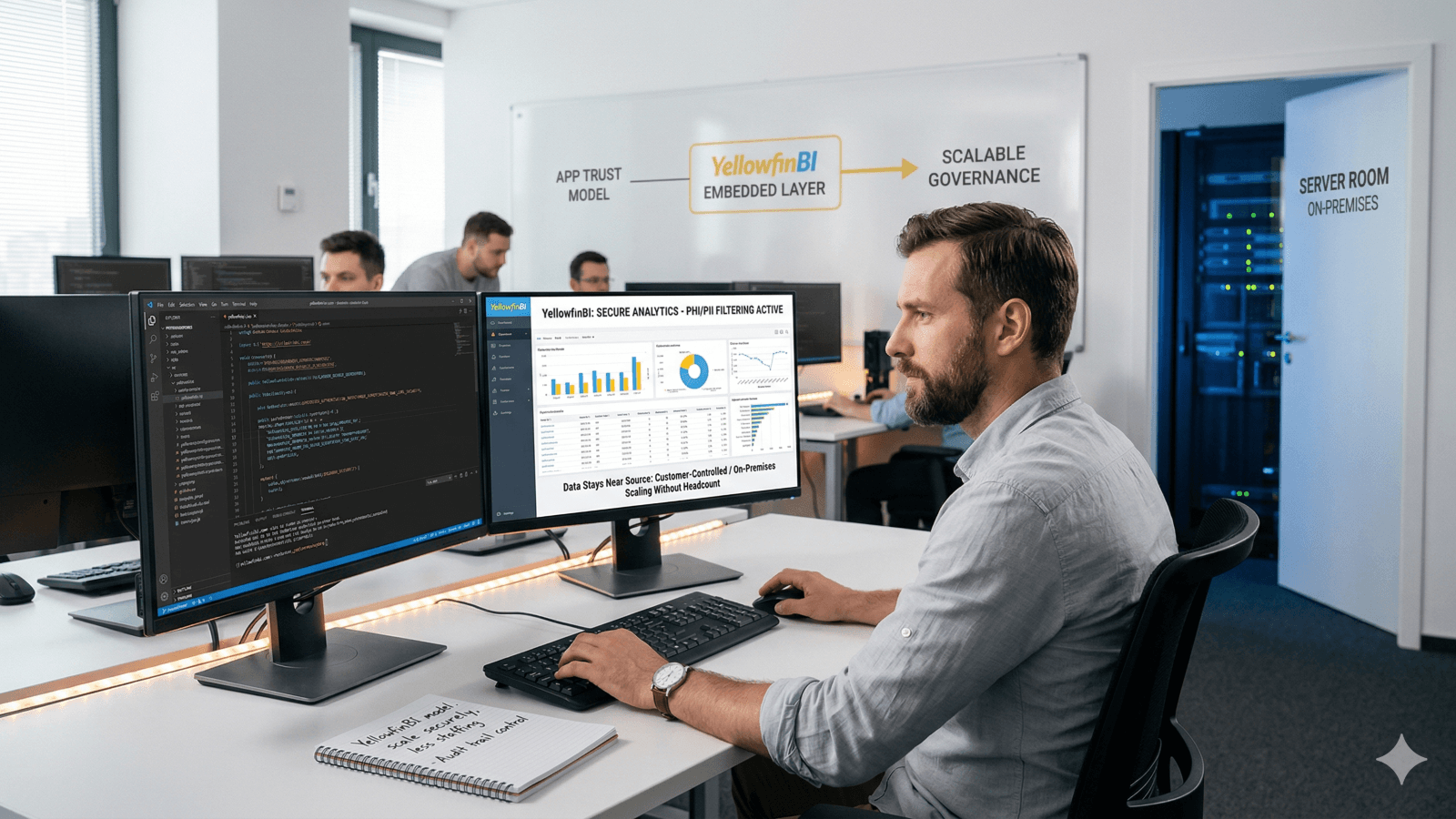
The chart is rarely the problem. The risk sits in the path that feeds the chart. That includes hosting, APIs, tokens, AI calls, logs, and copied datasets. If those pieces are loose, the dashboard becomes a data leak with a nice interface. That is why YellowfinBI’s position on on-premises embedded analytics matters. Its model keeps governance close to the source instead of bolting it on later. See YellowfinBI’s own guidance in Embedded BI: Why On-Premises Embedded Analytics Beats Third-Party BI for Data Security.The Main Risks in Embedded Analytics for Sensitive Data Environments
Data transit, API exposure, and row-level security failures
The first risk is raw data moving through more systems than needed. Every extra hop adds another custody point. Even with encryption, the surface still exists. Misconfigured endpoints, weak token handling, and exposed APIs can turn a simple embed into an open door. Row-level security can also fail in multi-tenant setups. If filters are off by one rule, users can see records meant for another tenant, another client, or another care team. That is why sensitive environments need controls that sit inside the app trust model, not beside it. YellowfinBI’s on-premises and customer-controlled hosting model reduces unnecessary transit and keeps sensitive processing near the source. That is a cleaner posture than sending data through a vendor chain.AI, audit trail, and non-production sprawl risks
A newer risk sits in the AI layer. If AI features can see schema details, query context, or aggregate outputs without tight control, metadata leakage follows. Reveal’s write-up on Security With Embedded Analytics And Its AI Layer makes the point clearly: AI can widen the breach surface if it is not fenced in. Audit trails matter just as much. If a system cannot show who queried what, when, and from where, compliance review gets messy fast. That gap is painful in finance and healthcare. Non-production is another quiet problem. Perforce notes that Protecting Sensitive Data in Non-Production Environments ties data copies in dev and test to major exposure. Their research points to 60 percent of cases seeing breaches or losses tied to sensitive data in non-production, while 54 percent report slower cycles and 45 percent report lower quality from compliance friction. The fix is not more copies. It is in-place masking and tighter analytics workflow controls.Why Bolted-On BI Often Fails in Regulated Industries
Encryption helps, but it does not fix everything. It does not stop exposed endpoints. It does not stop bad configuration. It does not stop token theft. It does not stop cross-tenant leakage when the app logic is wrong. That is why the real goal is attack-surface reduction. Sensitive environments need fewer hops, fewer third parties, and fewer blind spots. A bolted-on BI layer often adds the exact problems it was meant to solve.
Why hiring more people is not the scalable answer
Many firms react by hiring more analysts, admins, and security staff. That works for a while, then costs climb and coordination slows. Analytics should not need a growing control room just to stay safe. A better model gives you built-in governance, inherited app authentication, native policy enforcement, and less need for custom retrofits. That is a leadership call, not just a tooling choice. CEOs, CTOs, and CIOs should ask a simple question: does the analytics layer cut operational drag, or does it add more of it?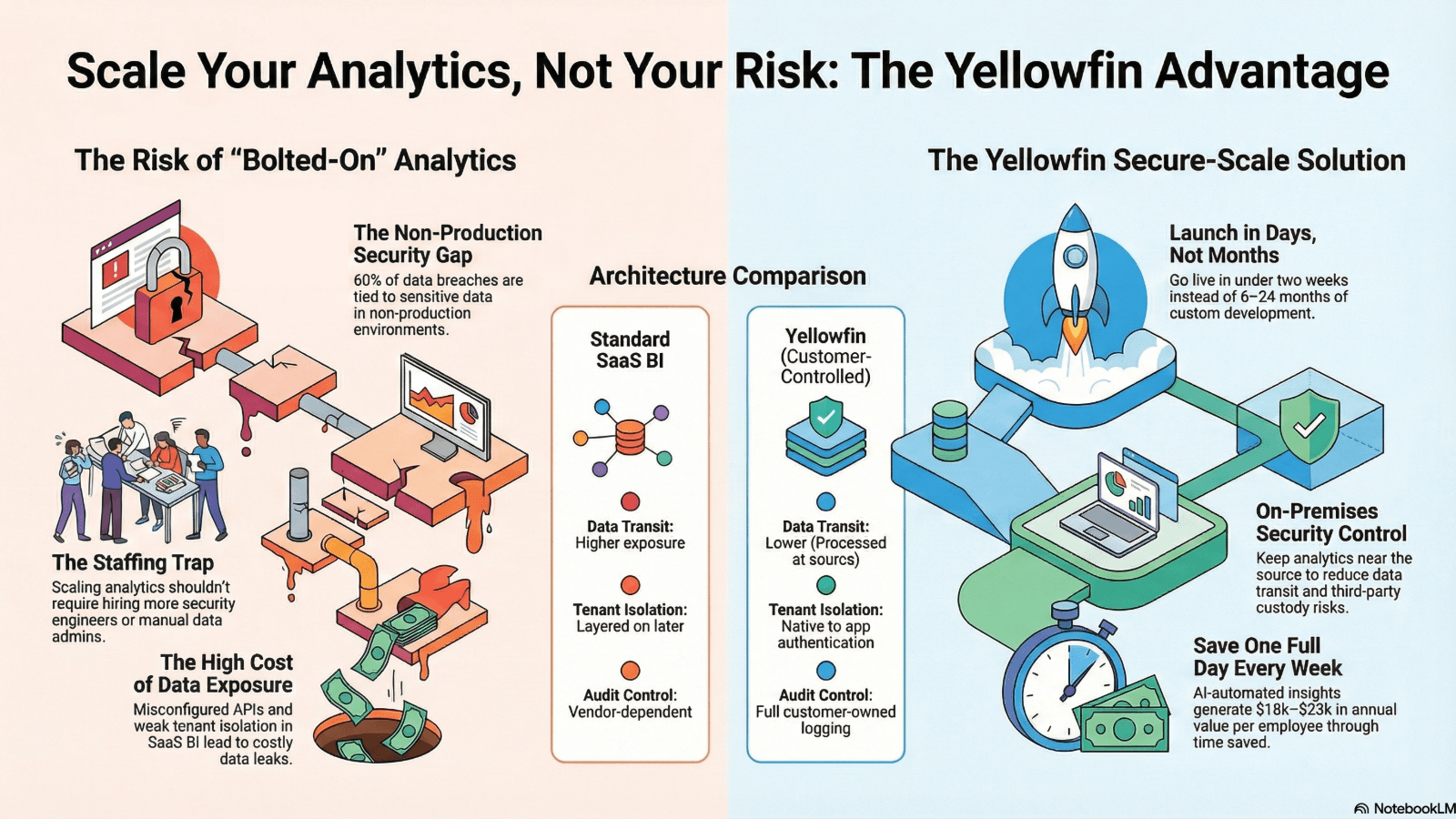
YellowfinBI's Security Model for Sensitive Data Environments
On-premises and customer-controlled deployment as the core differentiator
YellowfinBI’s main message is direct. Keep analytics closer to the data and under customer control. That matters for regulated data because it reduces transit, cuts third-party custody chains, and fits internal security standards more easily. This also makes compliance posture more predictable. When hosting, logging, and policy layers sit inside the customer environment, security teams get fewer surprises. YellowfinBI discusses this approach in Security Considerations When Choosing an Embedded Analytics Provider, including supply-chain and deployment risks that matter under frameworks like NIS2.Embedded controls that support secure scaling
The controls that matter most are practical ones:- row-level security
- app-level authentication inheritance
- tenant isolation
- configurable encryption
- audit logs with user and time context
- hardened SDK and API handling
| Capability | Bolted-on SaaS BI | YellowfinBI on-prem / customer-controlled embedding |
| Data transit exposure | Higher | Lower |
| Tenant isolation | Often layered on | Native / closer to app auth |
| Audit trail control | Inconsistent | Customer-controlled logging |
| AI endpoint control | Vendor-dependent | Customer-owned options |
| Compliance customization | Often retrofit-based | Built into deployment model |
Industry Perspective: Secure Analytics as a Governance Strategy, Not an IT Tax
The recommended point of view for the article
In sensitive environments, analytics should be treated as a governed product capability, not a separate BI layer. That framing changes the work. It reduces shadow copies. It cuts tool sprawl. It lowers manual oversight. It also keeps executives focused on business use, not constant cleanup after security mistakes.Messaging focus to reinforce throughout the article
The core message is simple. YellowfinBI helps teams scale analytics without scaling risk or headcount. The secondary message is just as important. Security and compliance are not blockers to embedded analytics. They are design requirements. For CEOs, that means faster decisions without hiring drag. For CTOs and CIOs, it means fewer architecture compromises. For analysts, it means trusted access without endless governance delays.Use Cases and Proof Points for Finance, Healthcare, and Other Regulated Sectors
Healthcare under HIPAA and privacy-sensitive operations
Healthcare teams need dashboards for operations, staffing, and care flow. They do not need broad PHI exposure. Embedded analytics can support these use cases if row-level security and audit logging are built in from the start. That matters in HIPAA settings where even internal users should only see the records they need. YellowfinBI’s customer-controlled model fits that pattern well.Financial services, insurance, and multi-tenant applications
Finance and insurance teams handle PII, account data, claims data, and strict tenant boundaries. A small leak can become a regulatory event. Multi-tenant SaaS systems face even more pressure because one session mistake can spill into another tenant’s view. YellowfinBI’s on-premises and isolation-first model gives teams more control over where data lives and who can see it.| Industry pain point | Business risk | Embedded analytics requirement | YellowfinBI-aligned answer |
| HIPAA/PHI access | Patient data leakage | Fine-grained access control | App-auth inheritance + RLS |
| Finance/PII | Regulatory violations | Auditability + isolation | On-prem deployment + logs |
| Multi-tenant SaaS | Cross-tenant exposure | Per-view separation | Hardened embedding model |
| AI-enabled insights | Metadata leakage | Controlled AI endpoints | Customer-owned routing options |
What Decision-Makers Should Evaluate Before Choosing an Embedded Analytics Provider
The practical selection criteria
Before choosing a provider, ask five questions.- Where does it run, on-prem, in a VPC, or fully hosted SaaS?
- What security controls exist for RLS, encryption, token handling, and logs?
- How does it fit HIPAA, GDPR, and NIS2 needs?
- Where do prompts, outputs, and context go in AI features?
- Does it reduce staff load, or add more custom work?