What is Data Security? - The Role of Analytics in Data Protection
Data security (or data protection) is a term often used in the context of analytics and business intelligence (BI). It encompasses a number of different policies, processes and technologies that protect an company's cyber assets against data breaches and threats.
But what does all of that really mean, in relation to BI specifically?
With so many different types of data security offered today, it’s naturally a broad topic that requires a deeper dive to gain a proper understanding of its many facets, and the key differences between it and other related terms, like data governance and data privacy.
In this blog, we break down what data security is in greater detail, to help you better understand its purpose, benefits for your business, and the many forms it takes in analytics solutions today.
What is the meaning of data security?
Data security refers to the practices, processes and tools that help organizations protect sensitive digital information, both in transit or at rest, from unauthorized access, disclosure, theft and tampering.
When used in the context of BI and analytics solutions, data security is the capability of the software solution in question to enable platform-wide protection policies, encryption, identity and access (IAM) and authentication controls, and auditing and administering of users and their data permissions. These capabilities fall under many specific sub-categories of data security, including data encryption, data loss prevention (DLP), data resilience, and data destruction.

What does data security do?
Data security exists to ensure the confidentiality and integrity of important digital assets are kept intact, and to help businesses guard against potential data compliance, regulation and litigation cases due to a data breach - regardless of whether the threat is accidental or intentional in nature.
A business intelligence and analytics solution with robust data security capabilities built into its software suite typically allow businesses to:
- Continuously and reliably meet important data and information compliance regulations (eg. General Data Protection Regulation, or GDPR) to avoid compromised data costs; a data breach today can cost businesses up to US$4 million, according to Gartner
- Control administrative privileges over what datasets and analytic content (dashboards, stories, etc) are allowed to be accessed by which individual user or group at a granular system level - this is often referred to as identity and access management (IAM)
- Encrypt data in transit and at rest (data traveling between the source and the analytics solution being used by the user)
- Set roles that can be assigned to said users or groups for appropriate database privileges (ensuring only authorized people can access specific data)
With data growing in complexity in quantity across organizations, the need to have stringent control over how and where that data is accessed, shared and used - and who is allowed to do so - is absolutely necessary to ensure sensitive digital information is compliant with legal regulations and is protected from unintentional or malicious access.
Read More: Data Security and Compliance: 5 Essential Considerations
Data security vs data governance and data privacy: What’s the difference?
Data security is closely related to and often encompasses both data governance and data privacy, but it is helpful to distinguish both categories from the broader umbrella for a better understanding of their importance.
Data governance is the lifecycle management practices and accountability measures put in place that help upkeep business data available, reliable and usable for consumption, analysis and sharing across the organization. These guidelines ensure data quality and protection standards (controlling, managing, tracking) are consistently met. In the context of business intelligence and analytics solutions, data governance refers to the capabilities of the platform that help organizations maintain their existing processes, policies and ownership around their data, and manage how critical information is created, monitored and shared within the BI platform.
Data privacy is the frameworks and policies put in place by a business that specifically address individual and group permissions around the processing and consumption of data that contains sensitive information, such as personally identifiable information. It takes into account regulatory compliance obligations, consent and notice around the use of data with identifiable information. A business intelligence and analytics solution will typically include controls that allow organizations to protect its datasets from unauthorized access or malicious misuse, to maintain data privacy.
Who is data security for?
Data security is incredibly important for every modern business with a digital presence.
Security and risk management leaders are in charge of securing data, but once data goes digital it can be a challenge to maintain the security and privacy of sensitive information without the proper models, processes and solutions in place that can support data protection robustly.
With a rapidly increasing amount of businesses adopting cloud, multicloud and hybrid information technology (IT) infrastructure to migrate their databases and business and analytics workflows into the digital realm, the move away from on-premise only data architecture means traditional data security, centered around finding attackers, and past policies and frameworks are becoming outdated faster. Security, identity access and privacy management products that do not integrate or have siloed coverage of data assets and security functionality are also increasing in number, but rapidly outdated.
Ultimately, information can be named anything, and stored anywhere, or used in several ways that may not be initially envisioned or accounted for. Data security is difficult without an understanding of data or the platform it resides in. This is why solutions that make it easy to carry over your existing security model and enhance it are essential - including analytics tools. Most importantly, tools that provide both access and controls over data to those who know what they are doing.
To secure data for advanced user cases that necessitate frequent internal and external data sharing, as well as to avoid disruption caused by siloed data security controls not designed to meet today's requirements, enterprise analytics vendors are recommended.
Where do I start with data security for my analytics users?
With any form of data access, the security, governance and privacy of the data you are using cannot be overlooked. The first place to start mitigating data risk in your organization and ensure quality and security is to manage data centrally. This is a big reason why businesses today are looking to enterprise analytics solutions that help keep data storage and analysis in one place.
But not all data analytics and business intelligence solutions vendors are equal in capability. Here are a few main considerations to keep in mind when assessing available BI vendors:
- Ensuring the BI solution you adopt has a well designed security model is a critical best practice. All analytics software should enable its end-users to share and act on data in a governed and secure way that keeps business information secure and only accessible by those who need it, and allow its administrators to put stringent protections, controls and permissions in place.
- With regulations surrounding data privacy and security being overhauled in recent years - such as Australia’s Notifiable Data Breach (NBD) act and Europe’s General Data Protection Regulation (GDPR) - it’s important to identify a solution that can help you meet these requirements, and understand the security powering your data access and consumption so you can ensure effective analytics efforts. Failure to do so can result in unintentional compliance breaches, unnecessary business risk and higher costs.
- Security layers powering modern dashboards typically begin with a protection framework that embeds role-based access across all aspects of the system. The best BI platforms give fine-grained control over to individual users and groups access to system functions and content. Start by assigning relevant users to the appropriate roles - either directly or by assigning them to a group - so permissions are established early on and content is accessible for the right people.
- Look and account for data security at the metadata layer, such as access filters, data source substitution and column level security to prevent sensitive information from being queried or run. Additionally, having measures such as Single Sign On (SSO) as part of your dashboards enables you to programmatically verify whether active sessions already exist before initiating a new dashboard session, reducing the need for manual log in and potential malicious attempts.
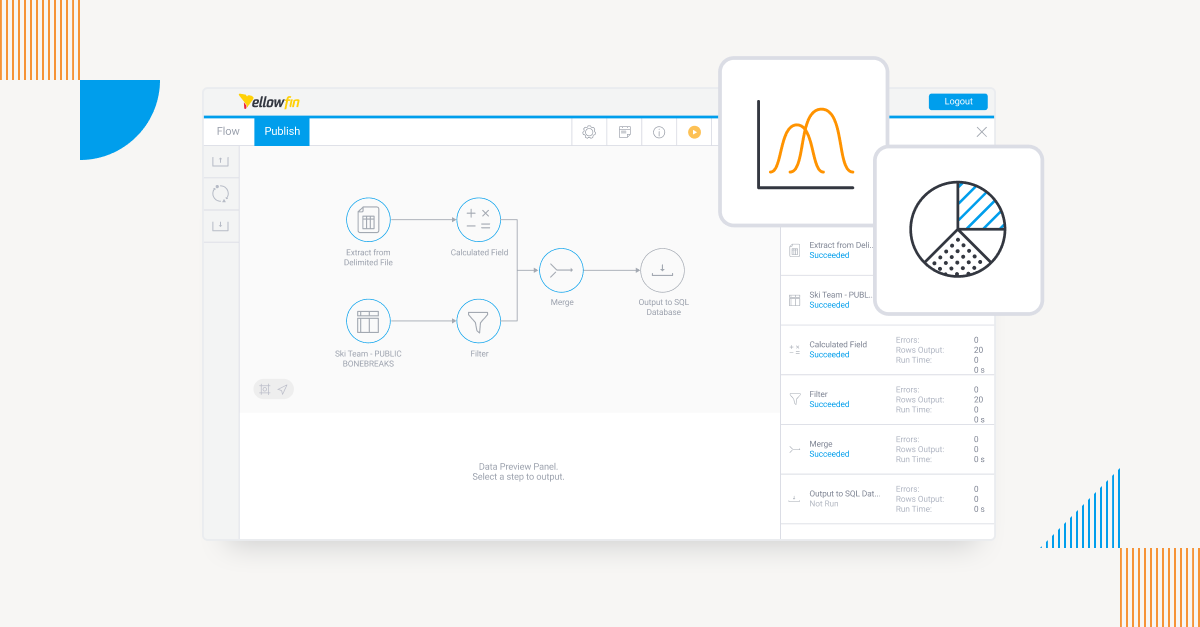
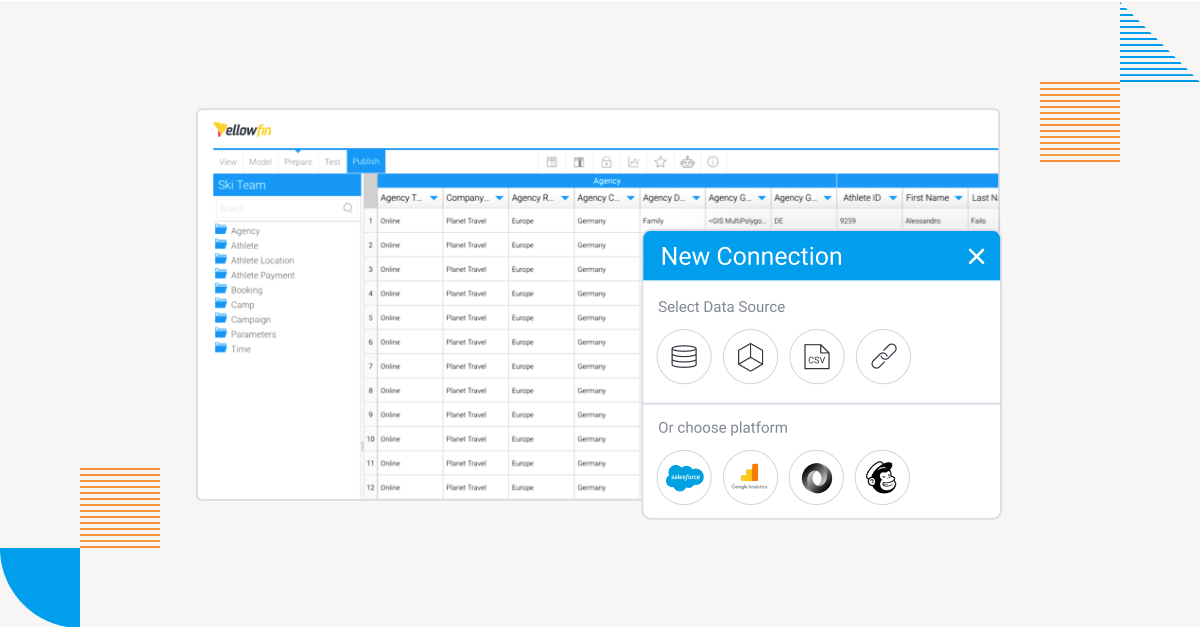
Yellowfin is a BI solution that meets all of these aforementioned considerations, with a comprehensive security model, up-to-date security & compliance accreditation, and functional user access and content protection controls.
Frequently Asked Questions About Data Security & Analytics
1. What is data security in analytics and business intelligence?
Data security in analytics refers to the safeguards built into BI platforms that protect data from unauthorized access, misuse, or breaches. This includes encryption, identity and access management (IAM), role-based permissions, auditing, and monitoring. In analytics environments, data security ensures that users only see the data they are authorized to access while still enabling insights and decision-making.
2. Why is data security important for business intelligence platforms?
Business intelligence platforms often centralize large volumes of sensitive business and customer data. Without strong data security, this data becomes vulnerable to breaches, compliance violations, and misuse. Secure BI platforms help maintain data integrity, ensure regulatory compliance, and protect organizations from costly legal and financial risks.
3. How does data encryption work in analytics tools?
Data encryption in analytics tools protects information both at rest and in transit. This means data stored in databases and data moving between sources and dashboards is encoded so unauthorized users cannot read it. Encryption is a core data security feature that prevents exposure even if data is intercepted or accessed improperly.
4. What is the difference between data security, data governance, and data privacy?
Data security focuses on protecting data from unauthorized access and breaches. Data governance defines how data is managed, controlled, and maintained throughout its lifecycle. Data privacy specifically addresses how personal or sensitive data is collected, processed, and shared in compliance with regulations. In analytics platforms, data security often acts as the foundation that supports both governance and privacy controls.
5. Who is responsible for data security in analytics systems?
While security and risk management leaders typically oversee data security, analytics administrators and data owners also play a key role. In BI environments, administrators manage permissions, roles, and access policies, ensuring that users can analyze data securely without exposing sensitive information.
6. How does role-based access control improve data security?
Role-based access control (RBAC) restricts data access based on a user’s role within the organization. In analytics platforms, RBAC ensures that users only view relevant dashboards, reports, or datasets. This minimizes the risk of accidental data exposure and helps organizations maintain compliance with data protection regulations.
7. What is identity and access management (IAM) in data analytics?
Identity and access management (IAM) controls who can access analytics platforms and what actions they can perform. IAM features include authentication, user roles, permissions, and group-based access. Strong IAM policies are essential for secure analytics, especially in cloud and hybrid environments.
8. How does data security help with regulatory compliance?
Data security enables organizations to meet regulations such as GDPR by enforcing access controls, encryption, auditing, and monitoring. Analytics platforms with built-in security features help businesses demonstrate compliance, reduce the risk of violations, and avoid costly penalties associated with data breaches.
9. What are common data security risks in analytics environments?
Common risks include excessive user permissions, lack of encryption, siloed security tools, unsecured data sharing, and outdated access policies. As analytics usage grows across teams, these risks increase unless data security is embedded directly into the BI platform.
10. How do enterprise analytics platforms support secure data access?
Enterprise analytics platforms provide centralized security models, fine-grained permissions, metadata-level controls, and features like Single Sign-On (SSO). Solutions like Yellowfin integrate security, governance, and analytics in one platform, allowing organizations to scale data access securely without sacrificing control or compliance.
Data security: Getting started with secure analytics
Discover Yellowfin's comprehensive data security suite, including its robust role-based access controls, multi-tenancy, certifications & content security.